David Rupprecht, Katharina Kohls, Thorsten Holz, and Christina Popper
Ruhr-Universität Bochum and New York University Abu Dhabi
Voice over LTE (VoLTE) is a packet-based telephony service integrated into the Long Term Evolution (LTE) standard. As of now all major telecom operators use VoLTE. To secure phone calls, VoLTE encrypts the voice data between the phone and the network with a stream cipher. Stream ciphers will generate a unique keystream for each call to prevent the keystream reuse problem.
We present ReVoLTE, an attack that exploits an LTE implementation flaw to recover the contents of an encrypted VoLTE call. This enables an adversary to monitor VoLTE phone calls. ReVoLTE uses a predictable keystream reuse. Ultimately, keystream reuse allows an adversary to decrypt a recorded call with minimal resources.
We provide an overview of the ReVoLTE attack, implications, and demonstrate the feasibility of a ReVoLTE attack in a commercial network. Furthermore, we publish an app that allows tech savvy people to track networks that are still vulnerable. Our work will appear at the 29th USENIX Security Symposium (2020) and all details are available in a pre-print version of the paper.

What does ReVoLTE exploit?
ReVoLTE attacks exploit the reuse of the same keystream for two subsequent calls within a radio connection. This weakness is due to an implementation flaw of the base station (eNodeB). To determine how wide the protection gap was, we tested several randomly selected radio cells primarily across Germany but also in other countries. The security flaw affected 12 out of 15 base stations.
How does the ReVoLTE attack work?
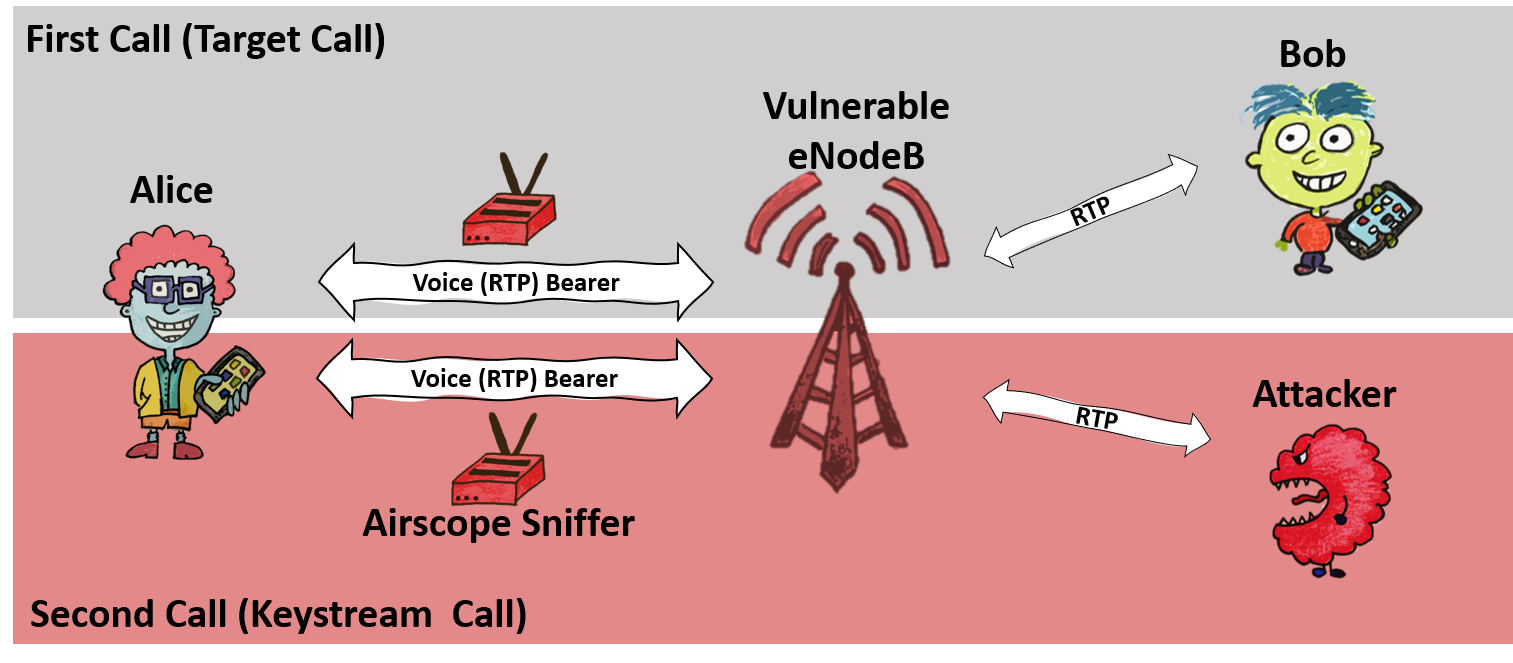
The purpose of the ReVoLTE attack is to eavesdrop on calls between Alice and Bob. We will call this call the target or first call. To carry out the attack, the attacker sniffs Alice’s encrypted radio traffic within the cell of a vulnerable base station. Immediately after the first call ends, the attacker calls Alice and engages her in conversation. We call this second call, or the keystream call. For this call, the attacker sniffs Alice’s encrypted radio traffic and records the unencrypted sound (known plaintext).
To decrypt the target call, the attacker must now compute the following: First, the attacker combines the known plaintext (recorded on the attacker’s phone) with the ciphertext of the keystream call. Thus, the attacker calculates the keystream of the keystream call. Due to the weak base station, this keystream is the same as the target (first) call. In the second step, the attacker decrypts the first call by extracting the keystream with the ciphertext of the first call. It is important to note that the attacker must engage the victim in a lengthy conversation. The longer he talks to the victim, the more content of previous communications he can decrypt. For example, if the attacker and the victim talked for five minutes, the attacker can later decode five minutes of the previous conversation.

Are my phone calls still vulnerable to eavesdropping through ReVoLTE?
To reduce the risk of eavesdropping, we notified providers about the attack vector through the GSMA Coordinated Vulnerability Disclosure Program process in early December 2019. GSMA has requested vendors to provide patches for affected base stations. As of the time of publication, those vendors should have provided patches, and providers are urged to install and configure them securely. Re-testing indicates that German operators have managed to install the patch. However, we need to consider the large number of providers and their large deployments around the world. Therefore it is important to increase awareness of the vulnerability. If you want to know whether your network is unsafe or not, you can test it with our app.
To demonstrate the practical feasibility of the ReVoLTE attack, we implemented an end-to-end version of the attack within a commercial network (which was unsecured) and commercial phones. We use downlink analyzer Airscope by Software Radio Systems to sniff encrypted traffic. Additionally, we use three Android-based phones that are controlled via ADB and SCAT to obtain known plaintext on the attacker’s phone. For a demonstration of these steps, please watch the video below.
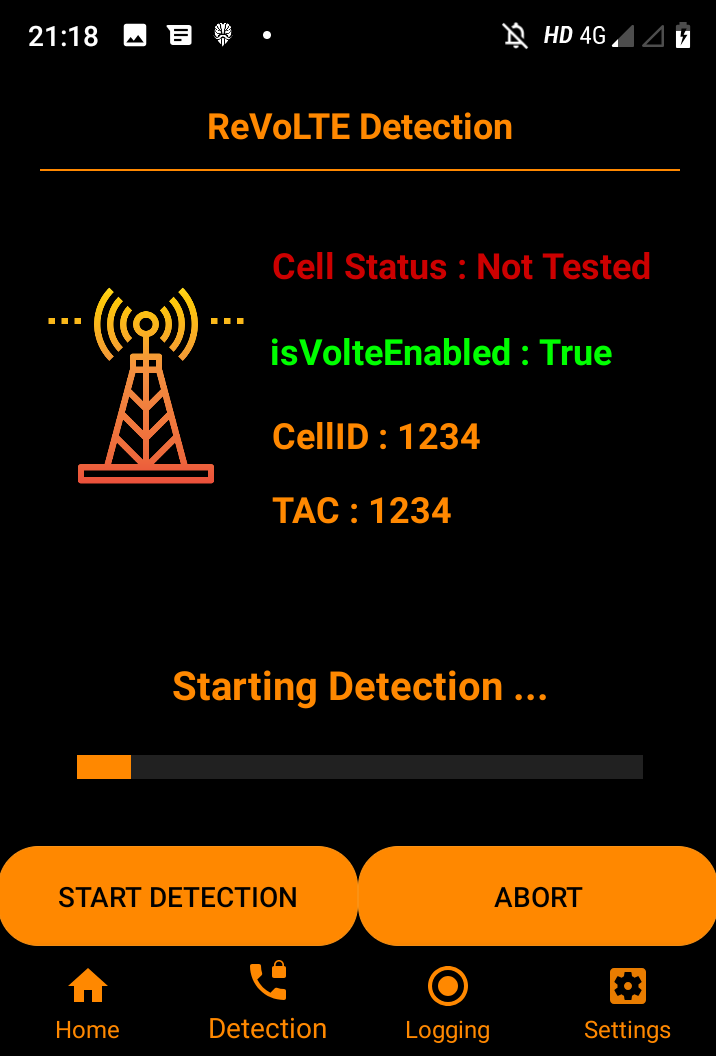
Is it possible to detect whether a base station is sensitive to ReVoLTE?
Yes, we (mainly Bedran) has developed an app that allows to detect whether a base station is vulnerable to a ReVoLTE attack. The app requires a VoLTE enabled Android phone with root access and a Qualcomm chipset. Please click here to visit the Github page regarding the Mobile Sentinel app.
abstract
Voice over LTE (VoLTE) is a packet-based telephony service integrated into the Long Term Evolution (LTE) standard and deployed by most telecommunications providers in practice. Due to this widespread use, successful attacks against VoLTE can affect a large number of users around the world. In this work, we present ReVoLTE, an attack that exploits an LTE implementation flaw to recover the contents of an encrypted VoLTE call, thereby enabling an adversary to spy on phone calls. ReVoLTE uses a predictive keystream reuse at the radio layer that allows an adversary to decrypt a recorded call with minimal resources. Through a series of preliminary as well as real-world experiments, we successfully demonstrate the feasibility of ReVoLTE and analyze various factors that critically impact our attack in commercial networks. To mitigate the ReVoLTE attack, we propose and discuss short- and long-term countermeasures to be implemented by providers and equipment vendors.
- ReVoLTE attack can decrypt 4G (LTE) calls to listen to conversations [1]
- ReVoLTE is an attack that allows intercepting encrypted calls in LTE [2]
- rebel attack [3]
- ReVoLTE attack allows hackers to listen in on mobile calls [4]
- ReVoLTE attack allows eavesdropping on encrypted 4G (LTE) calls [5]
- ReVoLTE attack encrypted voice call interception [6]