In October, I reported two security issues in Okta’s auth0/nextjs-auth0 project here and here. The latter bug, an OAuth parameter injection, allows several types of abuse, such as scoping tokens for unintended services, setting redirect_uri And scope Arbitrary values for leaking tokens, etc.
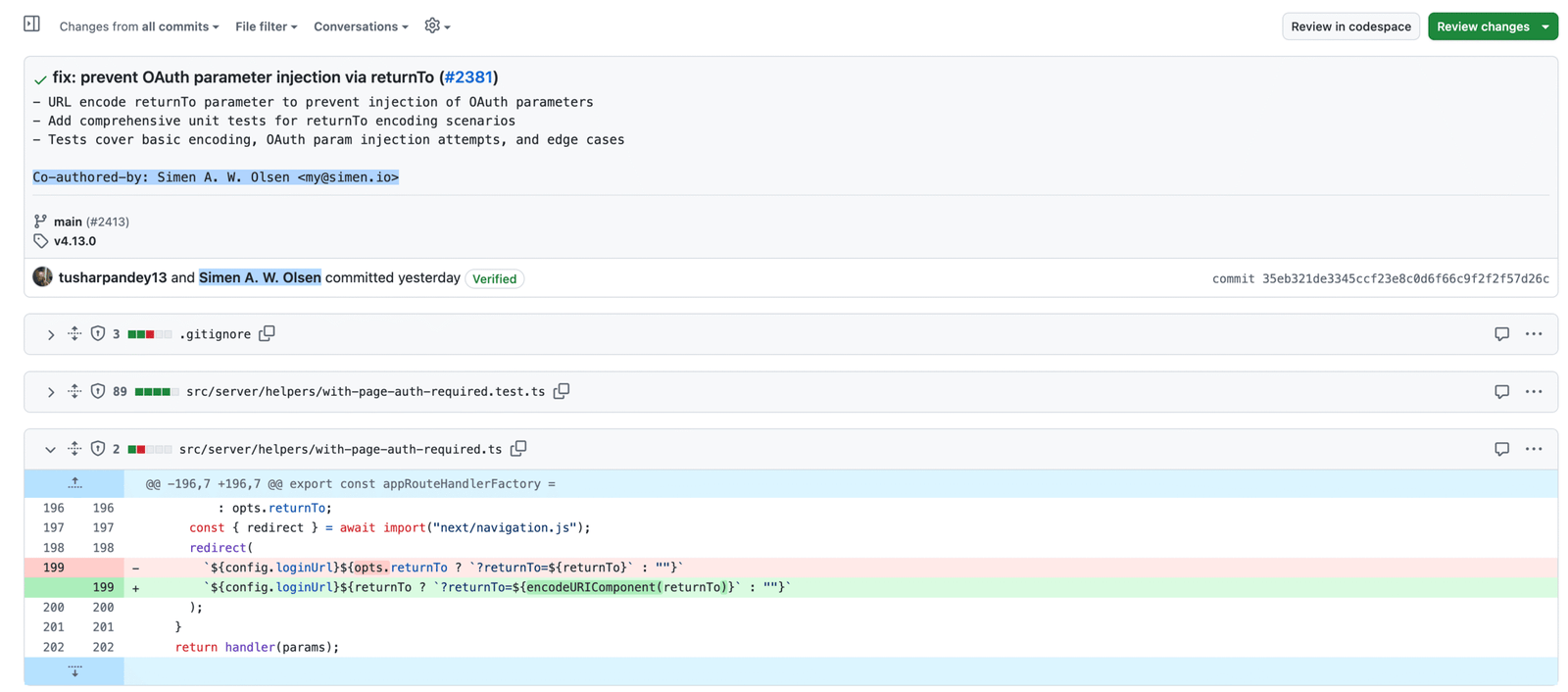
The patch was simple enough, so I opened a PR:
diff --git a/src/server/helpers/with-page-auth-required.ts b/src/server/helpers/with-page-auth-required.ts
index 41af2dfe..f07046b8 100644
--- a/src/server/helpers/with-page-auth-required.ts
+++ b/src/server/helpers/with-page-auth-required.ts
@@ -196,7 +196,7 @@ export const appRouteHandlerFactory =
: opts.returnTo;
const { redirect } = await import("next/navigation.js");
redirect(
- `${config.loginUrl}${opts.returnTo ? `?returnTo=${returnTo}` : ""}`
+ `${config.loginUrl}${opts.returnTo ? `?returnTo=${encodeURIComponent(returnTo)}` : ""}`
);
}
return handler(params);
All’s well that ends well, right? Obviously, no.
The PR was closed, 3 weeks later, by the maintainer, an Octa0 (an Okta company) employee, with the following comment:
This is superseded by change #2413. This was to ensure that the commitments were signed. The original contribution history has been preserved. So I am closing this PR now.
Hmm, let’s take a look He PR:
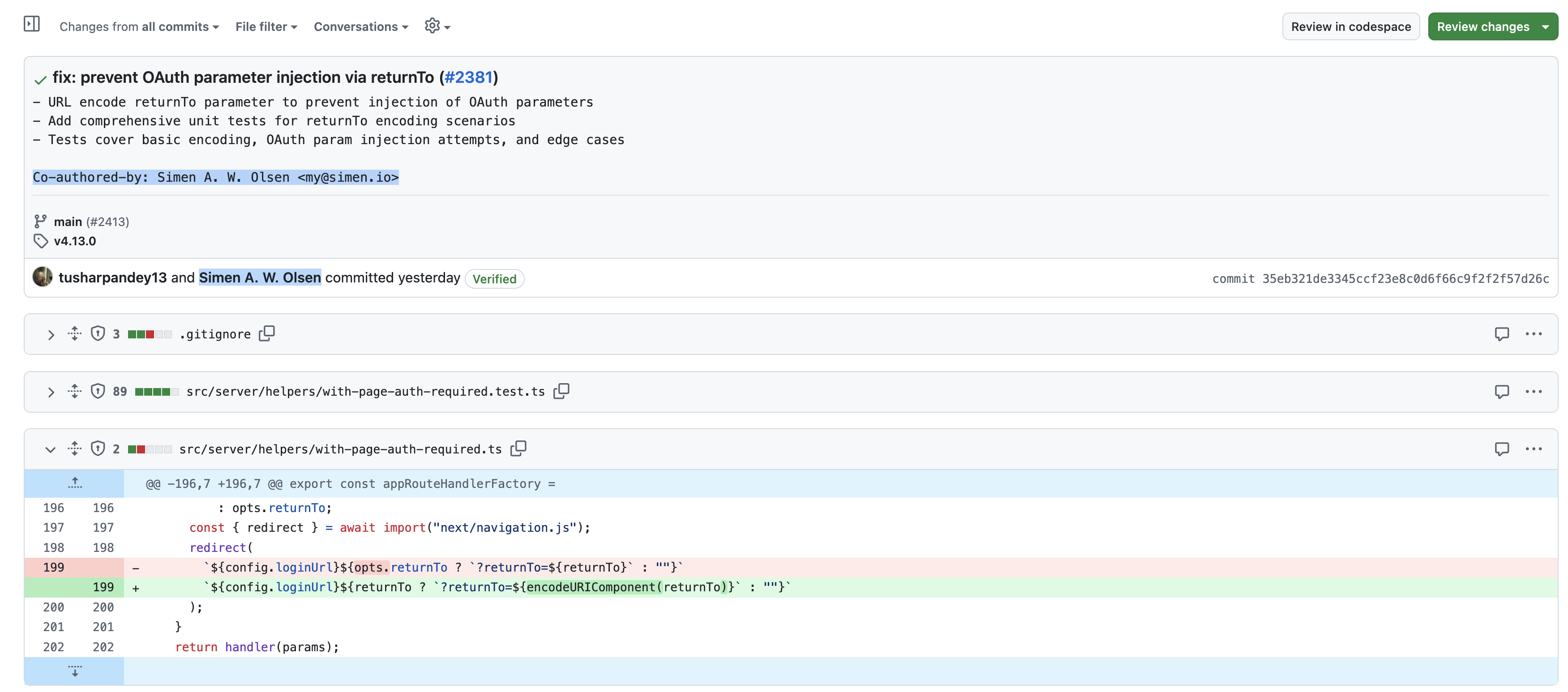 |
|---|
| auth0/nextjs-auth0 #2413 |
Hmm. That patch looks familiar. And who is Simen Olsen?
Emphasizing the attribution error, I replied:
History has been preserved
No, it is not so. I don’t know who “Simen AW Olsen my@simen.io” is, but it’s not me and my commit here doesn’t reference that name or email address at all. Was it AI generated or something else?
Of course, the answer was: yes. This was AI’s negligence.
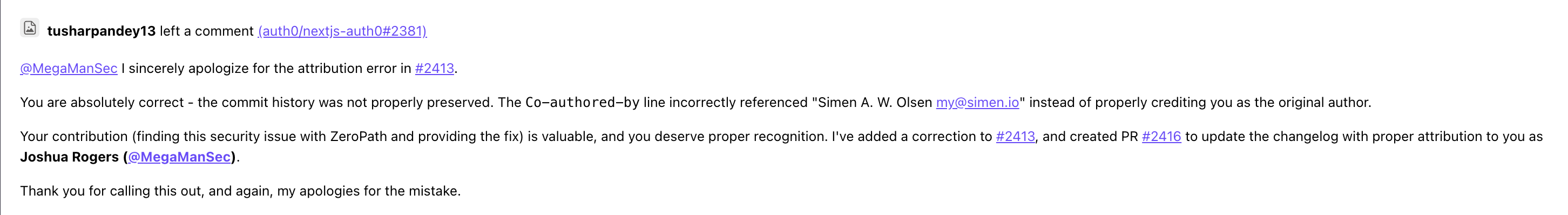
Hello @MegaManSec I sincerely apologize for this attribution error.
Can confirm that an AI workflow was used to create the rebased commit, which got confused with the OP description. I’ve added a fix to #2413, and will make sure the changelog gets updated.
Thanks for highlighting this, we will make sure it doesn’t happen again.
Not only did the maintainer explain the above, but they also used AI to generate the response! In a now deleted comment, he apparently used some AI to respond to my complaint:
 |
|---|
| auth0/nextjs-auth0 now deleted comment #2413 |
With Classic ChatGPT”you are absolutely right”, It is very disappointing that this developer used AI:
- Take my report/PR and commit it yourself.
- Used AI to commit it, removing my attribution.
- Used the AI to “apologize” for using AI, then said “it won’t happen again” – (yes right; please provide a detailed explanation of how you would ensure this, when clearly a 1-line code change is too much for your AI to handle without breaking).
- Refused to fix the commit by removing the invalid/AI-generated-slop description and adding mine back.
Actually, asking:
I would appreciate a force correction to the commit to properly include my information in the commit.
I was told they couldn’t change it. This sounds like copyright violation to me: taking someone else’s code, then changing the author’s name?
what i really like the most interesting is true How This also became AI slope. I can’t find any reference to the email address “my@simen.io” anywhere online. On GitHub, the only reference to this email address is from the Nextjs-auth0 PR. Simen Olsen has never contributed to the nextjs-auth0 repository as far as I can tell (searching) org:auth0 author:simenandre on GitHub), and it doesn’t even seem to be their actual email address. So was this some kind of AI hallucination? And why? The code change was small. I don’t fully understand it: I really get it Never Did some AI tooling fail like this and come up with someone else’s (fake) contact details. This is absolutely absurd; Are auth0’s engineers doing something extremely (extremely) Low quality local model or something else? If ChatGPT failed like this for me even once out of every thousand times, I would never use it again.
Finally, at the time of writing this, the auth0/nextjs-auth0 maintainer, Tushar Pandey, who made all these mistakes, has not fixed the attribution mistake in the commit history. Also, the first bug in this software that allowed arbitrary account hijacking has been fixed after 3 weeks, new versions of the NextJS-Auth0 software have been released, but Okta’s security people say “unless you make a video abusing this vulnerability, we won’t accept it as a security issue” – LMAO; “Yes, this is a vulnerability, we fixed it in the code, it can be used to handle accounts, but you need shoot a video“. Hilarious. This is another case to add to my list of ridiculous problems related to security issue reporting, which my next post will document.
Accurate weather forecast Kotor for today, tomorrow, and next week. Temperature, precipitation, wind, and humidity are all included. Follow the weather in Kotor and get up-to-date weather data online.
купить кольцо в москве https://kolca-pomolvka-msk.ru
Если вам нравится стиль провайдера Hacksaw Gaming – резкие бонуски, высокая динамика и слоты, которые часто держат в напряжении до последнего спина – загляните в наш Telegram. Мы ведём канал именно про Hacksaw: публикуем подборки лучших тайтлов, разбираем фичи (покупка бонуса, модификаторы, этапы бонус-раундов), отмечаем, какие игры больше “на разнос”, а какие спокойнее по темпу, и делимся новинками, как только они появляются. Удобно, если хотите быть в теме и быстро выбирать, во что сыграть сегодня.
Когда ищешь проверенные казино без верификации, главное – не попасть на сайты с “сюрпризами”: то вывод режут, то правила меняются на ходу, то поддержка пропадает. Чтобы не тратить время на перебор и ошибки, мы ведем Telegram-канал с подборками и краткими разбором условий: где проще старт, какие лимиты на вывод, какие платежные методы реально проходят и что сейчас работает стабильно. Ссылка на канал: https://t.me/s/rating_casino_russia/20
Качественное SEO https://outreachseo.ru продвижение сайта для бизнеса. Наши специалисты предлагают эффективные решения для роста позиций в поисковых системах. Подробнее об услугах и стратегиях можно узнать на сайте
Любишь азарт? пин ап казино вход предлагает разнообразные игровые автоматы, настольные игры и интересные бонусные программы. Платформа создана для комфортной игры и предлагает широкий выбор развлечений.
ремонт санузла в квартире ремонт ванны цена
ремонт ванной комнаты под ключ https://remont-vannoy-spb.ru
ремонта ванной комнате ключ ремонт ванны комнаты цена
Узнать больше здесь: https://armstroy72.ru
дизайн интерьера квартиры 25 кв услуги дизайнера интерьера квартиры
Старый паркет? https://shlifovka-parketa.ru профессиональное восстановление деревянного пола без пыли и лишних затрат. Удаляем царапины, потемнения и старое покрытие, возвращаем гладкость и естественный цвет. Используем современное оборудование, выполняем циклевку, шлифовку и лакировку паркета под ключ с гарантией качества и точным соблюдением сроков.
Details inside: https://www.upscalejourney.com/virgin-lady-gender-very-first-time-gender-porn-hub-lookup/
Today’s Summary: http://www.rosestudio.uk/2026/03/17/11-melhores-casinos-legais-em-portugal-como-deves-contar/
Лучшее прямо здесь: цены шлифовка лак паркета
office rentals in nyc office space new york city
Volvo в Україні https://spectehnika-volvo.mystrikingly.com/ екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
Нужны заклепки? заклепка вытяжная 5 сталь прочный крепеж для соединения деталей. Алюминиевые, стальные и нержавеющие варианты. Надежность, долговечность и удобство монтажа для различных задач и конструкций.
small office space for rent nyc office in new york
ответственное хранение материалов ответственное хранение товара
Лучшее путешествие джип тур авто горы, каньоны и побережье. Увлекательные маршруты, опытные гиды и яркие впечатления от путешествий по Крыму.
Do you trade cryptocurrencies? bitkelttrade.com registration automate your transactions and earn passive income. Smart algorithms analyze the market and help you make decisions. Increase your income and reduce risks with modern technology.
флаг с логотипом на заказ флаг с надписью на заказ